Information Security is a Big Deal these days, just as it should be. We are adding personal data (or personally identifiable data) to the internet at an unprecedented rate. Instagram alone sees 95 million new images per day. Whilst most would – and should – agree that the level of technology now accessible to the world is an incredible, and incredibly powerful thing, it behooves us to understand the risks that come with sharing any sort of information, particularly anything that can compromise one’s live in the “real world”.
There was a time when the boundaries between the ‘Internet World’ and the ‘Real World’ were pretty well defined. Growing up in the 90s and early 2000s as technology growth exploded, I’ve seen the shifts from that world to today’s fully integrated one. Personally I think it’s amazing how far we’ve come in such a short time, but with ease-of-use comes ease-of-loss.
I can now buy almost any commercially-available item in the world from the palm of my hand, by opening up my Amazon app and using my pre-saved credit card information to have anything delivered to me in just a few taps. I can pay for goods and services (up to a certain amount) using the phone itself as a payment method. I can order taxis, buy airline tickets, send and receive money, all alongside taking pictures and sharing them with friends and family.
This boundless freedom and possibility is exactly why you should be practicing good Digital Security. It’s why simple passwords aren’t “easy to remember” but the digital equivalent of leaving your front door open and your valuables on display. It’s why using the same password for everything is like using the same key for every lock – and keeping the master key under your front doormat.
It’s why Two-Factor Authentication (often referred to as 2FA, TFA, or Multi-Factor Authentication (MFA)) is incredibly important today, and why you should all be using it.
More and more websites and apps are now offering 2FA to their users as they realize that securing their users is in everyone’s interests. We all know that people love to complain more than praise – take a look at the TripAdvisor reviews for your favorite eatery if you don’t believe me. In this digital world, there’s no worse form of bad press than the world finding out that your customers got ripped off because someone broke into their accounts and racked up a $5000 bill.
It doesn’t matter that they post endless pictures of their new puppy, Doctor Bones, on Instagram, and that their password to every website is DoctorBones2018, thus making them an incredibly easy target. They were your customer and you didn’t protect them, so you get the blame.
Of course, in this scenario, everybody loses. Giant Conglomerate gets egg on their face because they let it happen, but Doctor Bones isn’t going to get any more of that fancy kibble he likes because his owners are now out $5000. Of course, that’s assuming that the hackers (I use that term loosely) didn’t also break into all of their other online accounts which it’s safe to assume they would have done.
If you’re still reading, congrats. Hopefully you’re realizing the dangers of keeping your data unprotected online. Well … hopefully you already realize that, but you get where I’m going with this.
So what is multi-factor authentication, how does it work, how is it different, and how is it better?
You’re already familiar with Single Factor Authentication, because you’ve been using it for years. Your email address or username for any service is your identifier; it’s who you are. In order to prove that you are who you say you are, you’re required to provide a password, that is, something you know.
In the old days, that was widely considered to be acceptable as a form of security. You tell the system who you are, and then prove that by giving it information that only you know; information that is verifiable against your account details.
As we’ve already discussed, in today’s modern world, a password is actually a very weak form of security. Security folks often refer to ‘attack vectors’ when discussing how secure or insecure a system is; imagine your account as the center of a mind-map. Each spoke connecting to it is a different way in which your account can be attacked and / or compromised. Each of these is an attack vector, and passwords have a lot of them.
You might tell a close friend, partner, or spouse, so that they can use an account on a service. You’ve immediately lost total control of that password, because they can then share that password on without restriction. They might write it down somewhere that someone else can pick up. Maybe it’s the same password you’ve got on other accounts, and now they technically have access to all of those systems too. Perhaps the same password is used for your email.
Let’s assume that all those things are true. You’ve shared your password and instantly given access to potentially anybody to your email, and thus the main portal for them to take control of your online identity, along with every other account you’ve ever signed up for using that address. Well done!
One great way to obviate some of these issues is to have a unique password for each account online. At least if one account is compromised, you can change its password and know that the attacker has no access to any of your other accounts.
In my experience, what that results in is the ‘Password Book’. I’ve dealt with more people than I can count in big corporations who keep every password written in a book. The concept of that book being stolen along with their laptop doesn’t seem to occur to them, but that would result in every account being compromised at once.
This process also encourages the use of simple passwords, which are easily cracked by computers, or repeatable patterns that make it easy for a hacker to guess at your other passwords once they’ve gained access to one or two of them.
So we’ve talked about how passwords are an incredibly insecure way of protecting your data. What can we do about it?
For years, I’ve been using 1Password from AgileBits. There are a number of other very good password management tools out there, several of which are free. Yes, 1Password is a paid app and service. However, in my years of using it I can safely say that it is worth paying money when it comes to securing your online identity. As we’ve discussed, these days an online identity IS your identity.
If your primary concern is keeping identity protection ‘as cheap as possible’ then you’re already thinking about it in the wrong way.
1Password allows you to generate a unique password for any login, then store it in a secure, encrypted vault, accessible on all your devices. What this ultimately means is that you need to remember one secure password. Just one. Once you’re into your vault, browser and app extensions mean that you can fill in login fields with the click of a button. You don’t even have to care what your passwords are anymore. Just have 1Password generate a long, secure, impossible-to-crack password for each site you’re a member of, and bask in the glow that comes with knowing that your identity is vastly more secure than it was before.
You might be content to stop there, but you shouldn’t. Huge sites like LinkedIn.com have had their entire user database stolen before, and no company is immune to the threat of espionage or theft.
Even though your data is now segregated, I’m fairly sure you don’t want anyone breaking into your accounts in the first place, right?
That’s where multi-factor authentication comes in.
What is it?
We’ve already said that passwords are something you know. That’s your first ‘factor’ in proving your identity. Multi-factor authentication adds additional ways of proving your identity. In some cases, it could be something you are, such as your TouchID / fingerprint or FaceID / retina sensors on your phones. The most common measure is something you have. This takes the form of a unique code, generated every 60 seconds.
How does it work?
You must be able to provide this generated code at login time. When you setup 2FA, you’re provided with a unique code and/or QR code. Feeding this to your 2FA-generating app results in the app generating unique codes that are unique to the online account you’re connecting to.
Now you’re providing something you know (password) AND something you have (the unique code), thus providing two factors of authentication to verify your identity.
How is it different?
By now this should hopefully be obvious. Whereas you can tell the world what your password is, you have no way of sharing a unique code that will last for more than 60 seconds. Whilst you can still share your account details with a third party, they only have a 60 second window in which to use those details. Once they log out and try again, they’ll need a new code.
How is it better?
Again, this should be obvious by now. It means that if LinkedIn.com leaks your data across the world and someone tries your username and password elsewhere, they’ll be required to also enter the unique code that only you can generate. In some cases an app might prompt you with a push notification to your phone. If you’re not logging into the account right then and there, you can dismiss it, safe in the knowledge that the third party is not gaining access to that account ! (Of course in this instance I’d strongly recommend you then go and change your password immediately.)
This sounds good, how can I get it setup?
Every site has a slightly different workflow for enabling 2FA, and yes you’ll need to spend some time and patience to get this setup. Let’s revisit the central premise though; this is about securing your identity. No time or money is too much here.
There are also several apps you can use for your 2FA codes. I’ve enjoyed using Authy, which currently secures my Discord, Google, Facebook, HMRC, and Circle Pay accounts.
However I’m now leaning in to using 1Password, with their somewhat-new but already-very-good 2FA support. What I love, and what prompted this article, is that the 1Password desktop application will scan your vault and tell you what logins you have setup that are not currently using the 2FA that those websites support.
Let’s see what that looks like.

You can see above 1Password for Windows 10. Watchtower is the name for 1Password’s proactive suite of tools design to protect your identities. As you can see, I don’t have a clean bill of health either!
Now Etsy is a very popular site that people use, so let’s take a look at enabling 2FA for Etsy. As you can see from the banner, 2FA is available but I’m not using it, so I’ll go ahead and click that ‘View Instructions’ link in the orange banner.
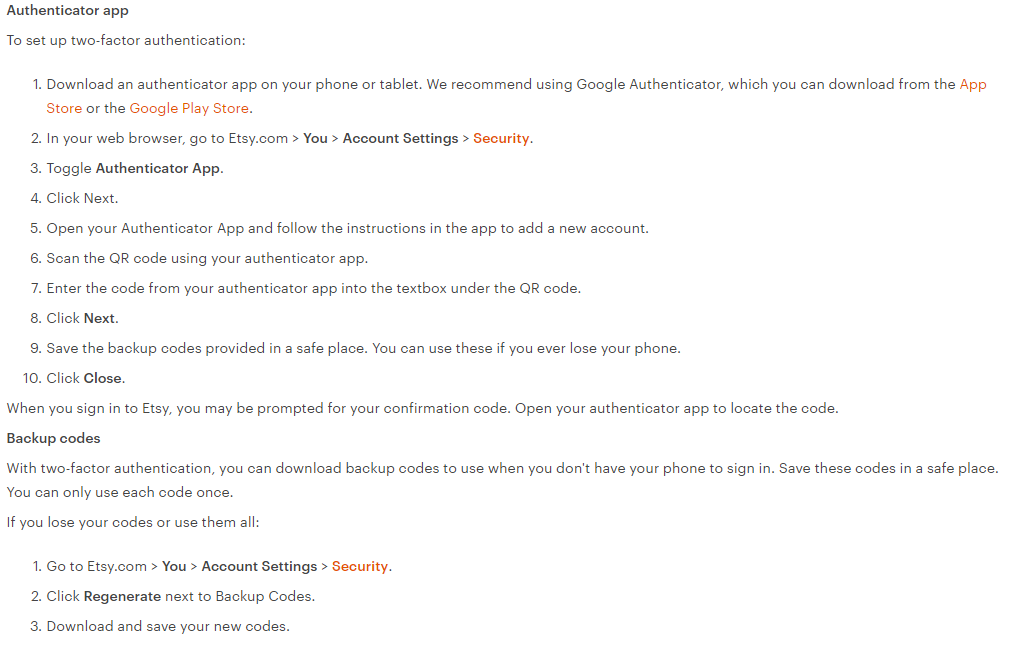
Google Authenticator is a very popular tool of choice. In my case I’ll be using 1Password and the workflow is slightly different, so I’ll login to my Etsy account and follow those instructions to get to my Security Page.

After toggling the 2FA to on, Etsy recommends visiting the App Store to get a 2FA Generator app. I already have one, so I click Next and get given this QR code (which I’ve muddled up just in case anyone scans it!) I won’t be scanning this with my phone (although I could), but behind the QR code is an actual string of text with 1Password is intelligent enough to pick up.
My next step is to edit the Login Item for ‘Etsy’ in 1Password and add a 2FA field.

Now your 2FA field is ready to accept some input. You’ll see the mini-QR code icon at the end of the field. With the QR Code from Etsy open, click the mini-QR symbol.
Depending on the website you might have to fiddle a bit here; some sites allowed ‘From My Screen’ and would automatically figure out what the code behind the QR image was. In Etsy’s case, I had to right-click and Copy the image, then choose ‘From My Clipboard’ in 1Password.
Click Save on the login entry, and find it again in 1Password. You’ll now see a new ‘2FA’ entry with a unique code and a countdown. In Etsy’s case the countdown is 30 seconds, which is the maximum length of time that code can be used.

Your penultimate task is to take the code from 1Password and enter it back to Etsy’s site under the QR code. Think of this as a handshake to confirm that the correct code is now being generated.
Finally, the site will give you ‘backup codes’. These are codes you can use to access your account in case your 2FA app is broken or unavailable for some reason.
KEEP THESE SAFE! They are important, but they basically bypass the whole 2FA process we’ve just gone through, so they must be treated with care.
How does it work day-to-day ?
What’s the deal, Etsy?
I was going to record a quick video to show you how the login process now works with 2FA, and in doing so discovered something that’s not-so-great. After logging into Etsy’s mobile app (and website) one with the 2FA code, logging out and back in no longer requires the code.
Checking Etsy’s page says the following:
You’ll be prompted to provide the code:
-Etsy
– When you sign in using a different browser or on a new device
– Every 30 days
In my view this is not the correct implementation of 2FA. It should be used at each and every login. I’ll setup another 2FA app and use that for a quick video instead, posted above.
SMS = No good
A lot of services, including Etsy, will allow you to use SMS (text messages) to have a 2FA code sent to you. If this is the only method available I’d suggest it’s better than nothing, but barely.
As you’ll see above, 1Password is using my face to authenticate me, otherwise it would be asking for my super-secure password. Let’s assume my phone was stolen and they learned the PIN (thus bypassing facial recognition), they still can’t get into my 1Password.
SMS delivery of 2FA completely skips over that, delivering a code directly to the phone. It’s bad. There are further vulnerabilities at play which I won’t go into here. The one thing you need to know is that SMS 2FA is almost worthless and if you have any other option, that’s the one you should employ.
